Post-quantum roundup | Week 8, 2026 - Demystifying quantum risk
A weekly roundup that prepares technologists for the quantum computing revolution and the post-quantum world
The Post-Quantum Weekly Roundup prepares technologists for the quantum computing revolution and post-quantum world.
This week’s post-quantum roundup focuses on demystifying quantum risk. While I believe in quantum risk, I’m still concerned about the rise of overexaggerations and broad claims among quantum “influencers.”
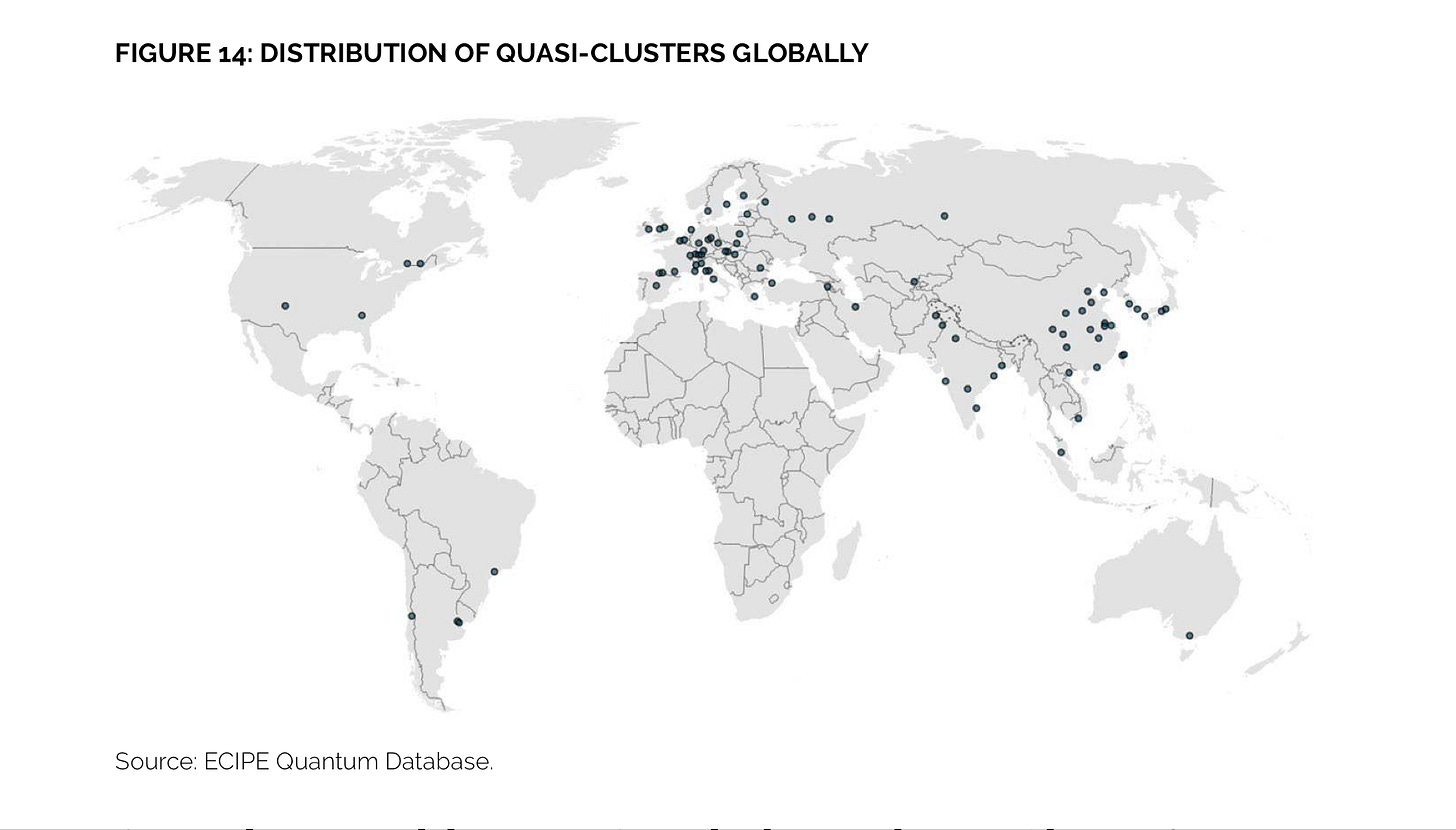
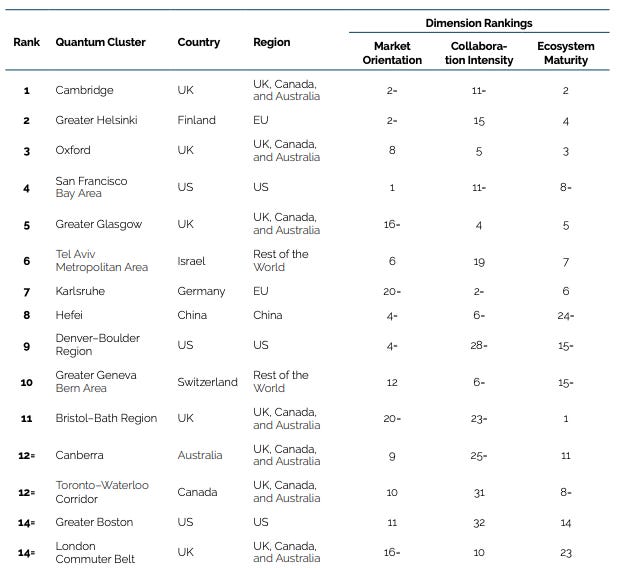
Also, I’m finally back in Seattle after traveling and visiting family over the past few weeks. Speaking of traveling, the European Centre for International Political Economy recently published a new ranking of 86 quantum computing hubs worldwide. Which quantum hub would you like to live in (or do you already live in)?
My picks are San Francisco (a great startup ecosystem), Helsinki (a safe city), and Seoul (a great culture. I love their music!)!
Definition of the Week
Mosca's theorem, developed by Dr. Michele Mosca of the University of Waterloo in Canada in 2015, explains the severity of quantum risk. The theorem has been cited more frequently in the past few months as quantum risk has become more severe.
The theorem states that cryptographic secrets break when:
The total duration in which the data must stay secure (x), plus the time needed to migrate to quantum-proof systems (y), exceeds the time required to develop a cryptographically relevant quantum computer (CRQC) (z), or a quantum computer that can efficiently break widely used public-key encryption.
We should worry because a CRQC will be available before all systems are migrated, and standard cryptography will start to fail when:
x + y > zWe should actively work toward post-quantum migration, but we have buffer time until cryptography fails, when:
x + y < z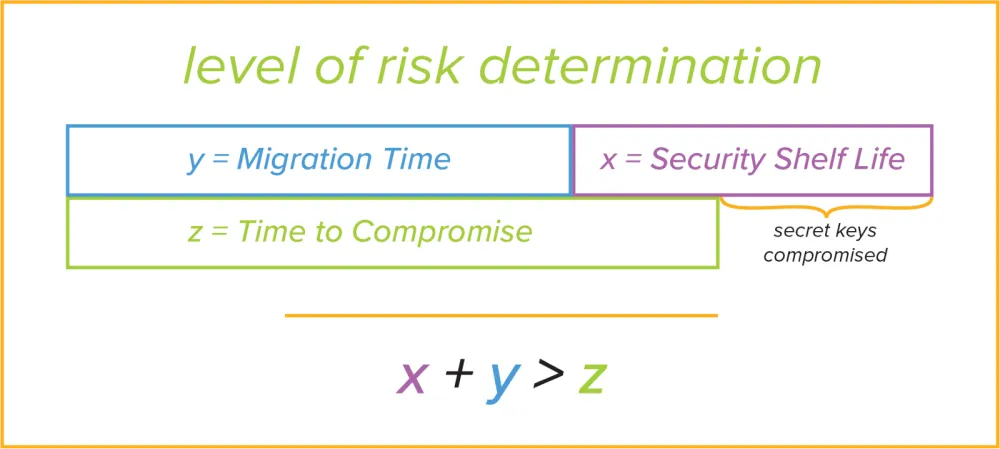
Suppose a hospital encrypts patient genomic data today using RSA and must keep it confidential for 20 years due to privacy regulations and long-term sensitivity. If it realistically takes 8 years to audit systems, update hardware, certify software, retrain teams, and fully migrate to post-quantum algorithms, then:
x = 20
y = 8
x + y = 28
If a CRQC capable of breaking RSA emerges in 15 years, as the U.S. National Institute of Standards and Technology (NIST) believes it will:
z = 15
Then 28 > 15, meaning that the genomic data will likely be leaked by hackers who will use quantum computers to break RSA encryption.
How do we actually know when a CRQC will be ready?
The direct answer is that we don’t, but we can still estimate.
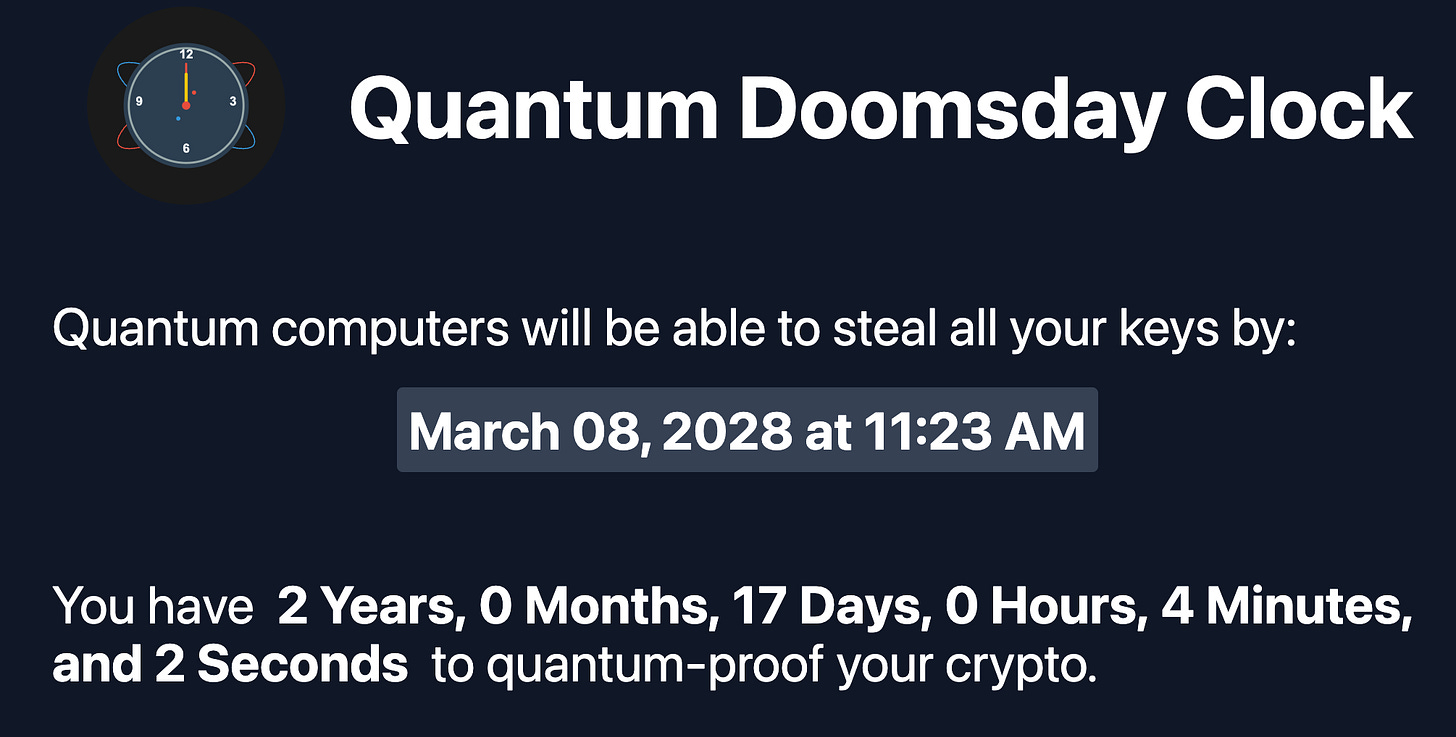
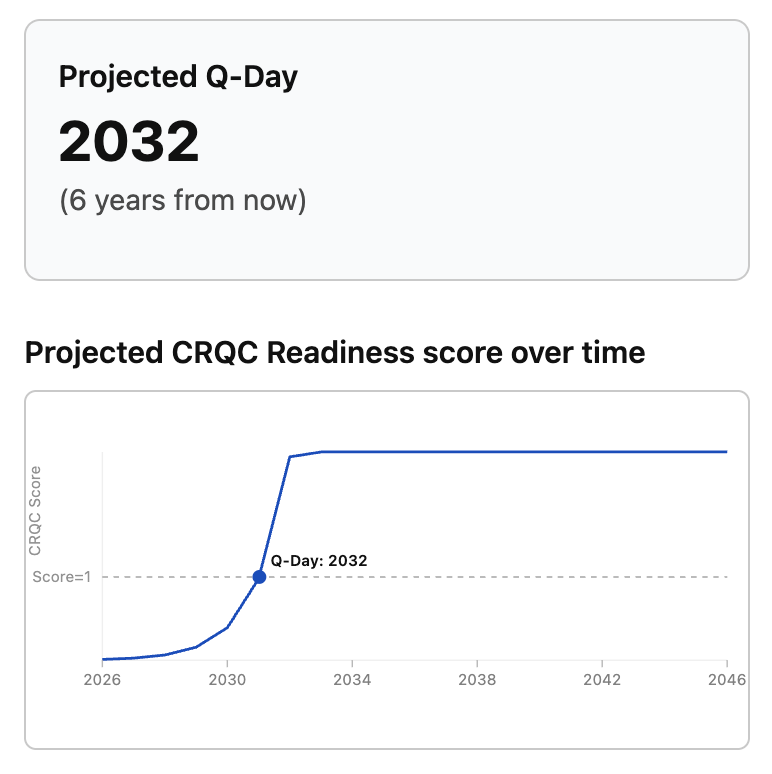
Countdowns to when a CRQC will be ready, or “Q-Day” estimates, predict when a defined number of logical, error-free qubits, as claimed by specific academic research to be needed to break a popular cryptographic scheme, will be available, based on trends in the number of available logical qubits.
The challenges with this methodology are that:
Academic research varies on the defined number of logical, error-free qubits necessary. The range is 1,700 to 6,000 logical qubits to break RSA encryption, and sensational countdowns tend to pick the lowest number.
The number of available, logical qubits does not necessarily grow at standard rates.
Examples of Q-Day countdowns, which are four years apart in their estimations, and their varying methodologies:
Quantum computers will advance, but how fast you think they’ll progress depends on the academic research you follow.
Academic Paper of the Week
Webster, P., Berent, L., Chandra, O., Hockings, E. T., Baspin, N., Thomsen, F., Smith, S. C., & Cohen, L. Z. (2026, February 12). The Pinnacle Architecture: Reducing the cost of breaking RSA-2048 to 100 000 physical qubits using quantum LDPC codes. arXiv.org. https://arxiv.org/abs/2602.11457
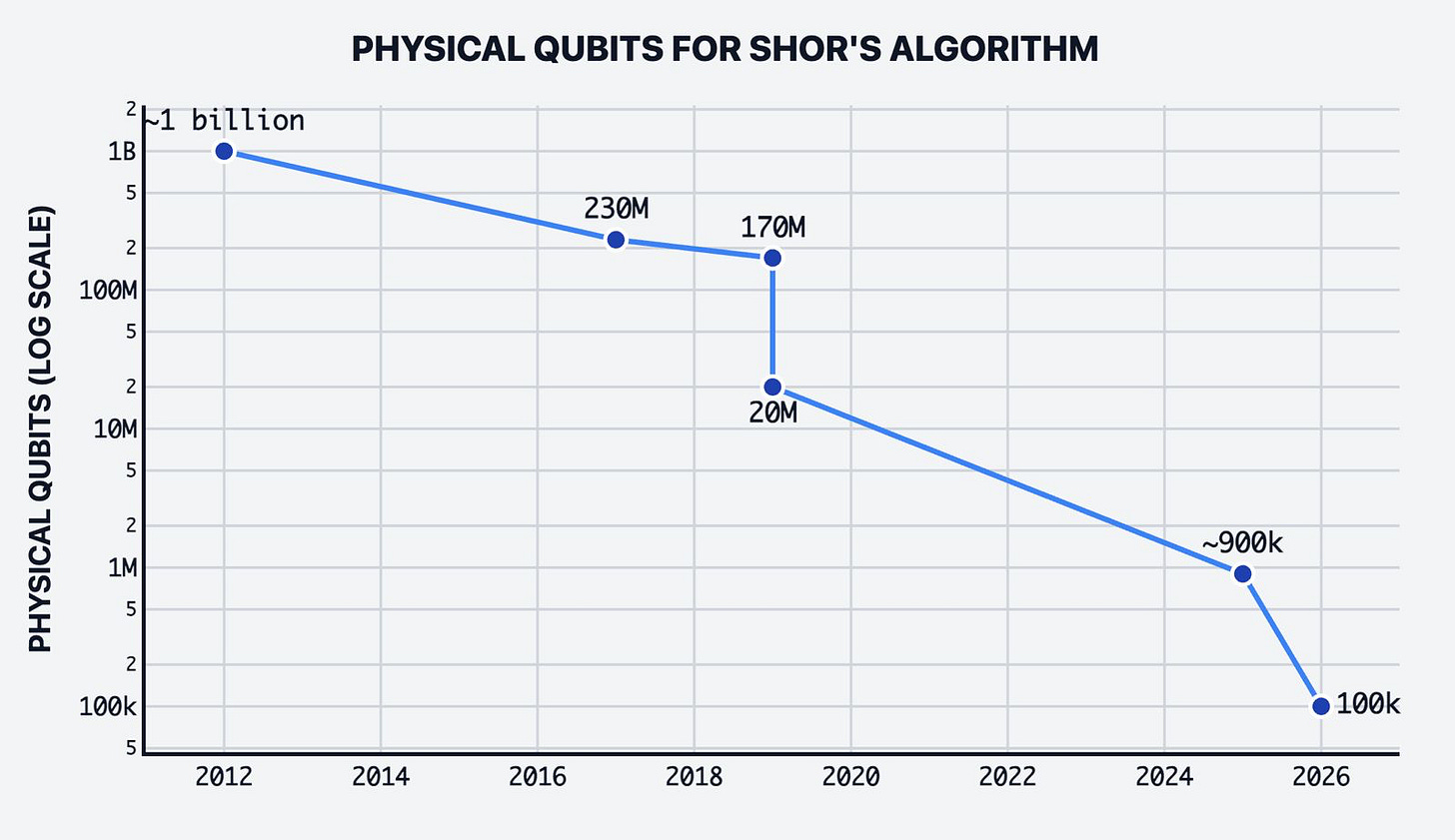
Researchers at Iceberg Quantum, a private company based in Sydney, Australia, that designs full quantum systems, claimed they can break RSA encryption with only 100k physical qubits using a new technical architecture, far fewer than the 900k qubits previously estimated in 2024.
Physical qubits are error-prone, while logical qubits are created by grouping physical qubits to protect them against errors and are more reliable for computation.
This article was widely shared within the post-quantum cryptography community as a major breakthrough, often without context. It’s an interesting finding, but without context, it can be misinterpreted.
What is Pinnacle Architecture, the new technical architecture approach that Iceberg Quantum uses?
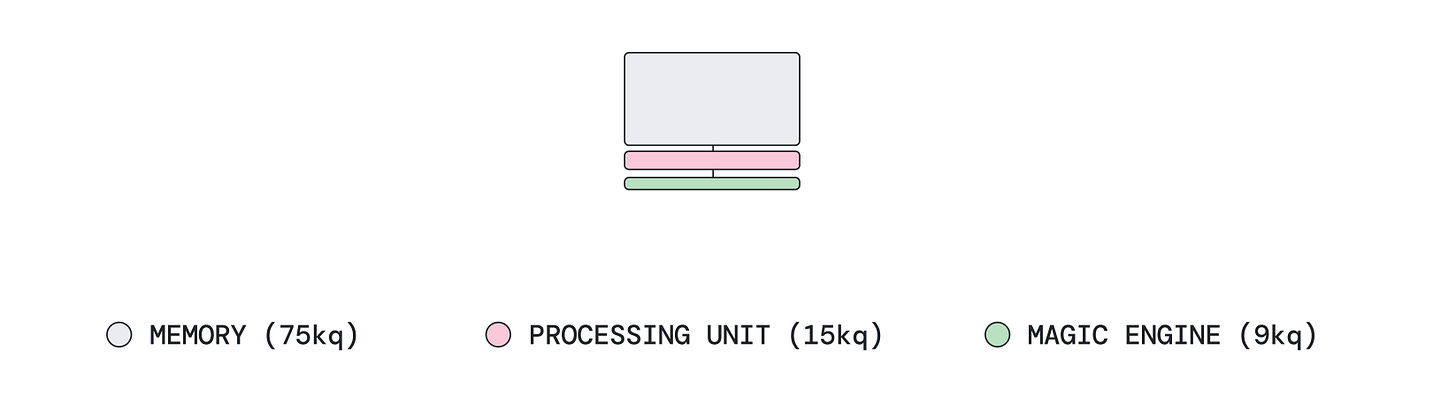
Iceberg Quantum proposed Pinnacle Architecture, a full-system, modular design, built around quantum Low-Density Parity-Check (qLDPC) codes. qLDPC codes are a newer family of error-correcting codes designed to protect fragile quantum information using far fewer extra qubits.
Pinnacle Architecture separates the quantum computer into specialized components: memory blocks that store logical qubits, processing units that perform computations, and dedicated “magic engines” that generate the high-quality special states required for complex operations.
How do researchers know that this can be done with 100k qubits when 100k qubits do not exist?
Like much research, Iceberg Quantum’s work relies on software modeling rather than using quantum computers.
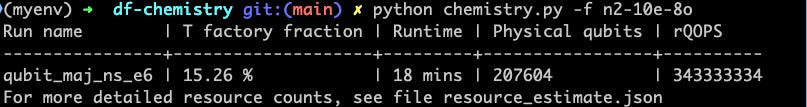
Researchers use quantum resource estimation, which involves software models that simulate the number of qubits needed for a specific task. For example, Microsoft’s free quantum resource estimation tool uses well-known predefined qubit parameter settings and common error-correcting schemes to estimate the number of qubits required for a task.
To calculate the energy associated with this chemical system within 18 minutes:
A nitrogen molecule where 10 electrons occupy the 8 orbital active space of the dissociated nitrogen at a 3 Angstrom distance
According to the Microsoft Azure Quantum Resource Estimation tool, it would require 207,604 qubits. 15 percent of qubits are dedicated to T-factories that produce T-states, which are valuable for low-error rates.
Adjusting the runtime, T-factory percentage, and other parameters could increase or decrease the number of physical qubits.
Researchers adjust the models to account for different error rates, operational speeds, and error-correction schemes. Understanding their methodology is important for assessing the likelihood of the result.
In the case of Iceberg Quantum, they used a model based on their pinnacle architecture, which was adjusted to different error rates and code cycles, or time to run a round of a quantum error correction code. They applied a quantum algorithm capable of factoring a 2048-bit RSA integer (or capable of finding two very large prime numbers whose product equals the RSA integer) to their qLDPC error-correction scheme and simulated the number of qubits required.
Using Shor’s algorithm, factoring an n-bit RSA number is known to take O(n³) gates. For a 2048-bit RSA integer, this typically meant 2048³ = 8.6 × 10⁹ gates, which required roughly 2,000-6,000 logical qubits and, under traditional error-correction assumptions, approximately 10–20 million physical qubits. Under Pinnacle Architecture, the breaking RSA required a similar number of gates and logical qubits, but qLDPC encoding reduced the physical qubit requirements, lowering the total to 100k physical qubits.
Runners-up for Academic Paper of the Week:
From the second breakout call on Post Quantum transaction signatures by the Ethereum Foundation:
Kudinov, M., & Nick, J. (2025, December 5). Hash-based signature schemes for Bitcoin. IACR Cryptology ePrint Archive. https://eprint.iacr.org/2025/2203
From PQCrypto 2026 accepted papers (which include many other great papers, too):
Centelles, A., & Mendelsohn, A. (2026, January 31). Abba: Lattice-based commitments from commutators. IACR Cryptology ePrint Archive. https://eprint.iacr.org/2026/148
Shared by Nic Carter:
Chevignard, C., Fouque, P.-A., & Schrottenloher, A. (2026, February 17). Reducing the number of qubits in quantum discrete logarithms on elliptic curves. IACR Cryptology ePrint Archive. https://eprint.iacr.org/2026/280
Video of the Week
A Coinage interview with Thomas Coratger, researcher at the Ethereum Foundation (EF), where he explains the quantum threat to Ethereum and potential technical challenges Ethereum might face migrating to post-quantum cryptography.
Next week, I’ll explain the technical requirements that his colleague, Justin Drake, uncovers in another, more technical podcast that was recently released.
Education
ARMChain is hosting an Introduction to Post-Quantum Cryptography webinar on Sunday, February 22nd, from 10:00 to 11:00 AM PST. Register here.
Build your first quantum support vector machine, a free virtual course on quantum-based support vector machines (SVMs), which supervised machine learning algorithm that classifies data by finding an optimal line. Register by the course time on Tuesday, March 3rd at 8:00 AM PST.
New Opportunities
Virtual
QFELLOWS is a flagship PhD and research community by Tectonic, a company building quantum-grade infrastructure for blockchains, that brings together quantum researchers, theorists, and experimentalists across disciplines to accelerate breakthroughs in post-quantum technology.
If you are interested in joining this community, please let me know if you want an introduction to the Tectonic team, as I am part of it!
Girls in Quantum Q-Hackathon 2026. For female students and researchers to create quantum projects in four tracks: Hardware (Energy Grid Optimization), Algorithm (Harmonic Oscillator), Finance/Quantum Machine Learning (Option Pricing), and Social Impact (Quantum for Good - no coding required in this track). Due: Apply by February 20 (Though the application says apply by February 23rd at 11:59 UTC).
Geography-specific
QIS 101: Foundations of Quantum Information Science is a six-week summer virtual program that introduces U.S. undergraduate and graduate students, recent college graduates, and academic educators to quantum information science and pays them a $500 weekly stipend for active participation. Due: Apply by April 3, 2026.
NQN Northwest Quantum Day in Seattle, Washington, USA, on Tuesday, April 14th, is a conference on the quantum ecosystem in the U.S. Pacific Northwest region. Come say hi if you are in town!
The Quantum Un-conference in Cambridge, MA, USA, on Saturday, February 21st, is a gathering of collaborative discussions on quantum computing. No speakers, only attendee collaborative discussions and presentations on topics such as:
What is quantum computing?
Learn and teach any quantum computing topic
What is your favorite qubit?
Following the Quantum Un-conference, the Sundai Quantum Hackathon in Cambridge, MA, USA, on Sunday, February 22nd, is a quantum hackathon with three unique challenge tracks:
Software (quantum algorithms)
Hardware
Physics (self-study the quantum mechanics behind quantum computing)
Previously shared opportunities
The full list of opportunities for paid subscribers.
Keep reading with a 7-day free trial
Subscribe to Realmscape - Anything Supercomputing to keep reading this post and get 7 days of free access to the full post archives.