How zero-knowledge proofs make quantum circuits “private”
Google Quantum AI used zero-knowledge proofs to conceal, yet confirm, quantum circuits that can break popular cryptography
This article is too long for email, so I recommend reading it in the app.
My main motivation for writing this article is to help readers understand how to interpret quantum computing papers, especially as the field becomes more mainstream and sensational claims spread widely.
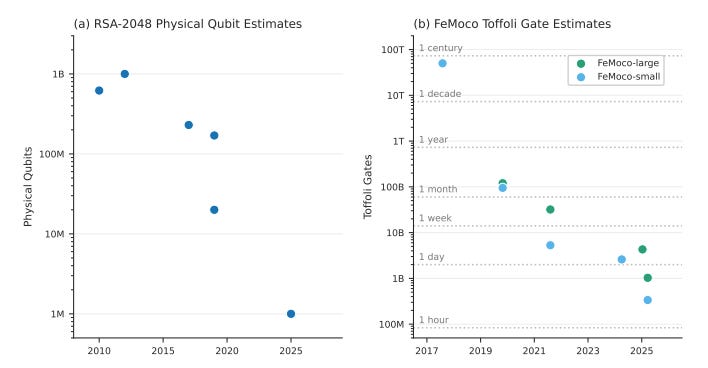
In a new white paper, researchers at Google Quantum AI, Stanford, and the Ethereum Foundation developed much smaller and less resource-intensive quantum circuits, or programs that run on a quantum computer, capable of breaking Elliptic Curve Cryptography (ECC).
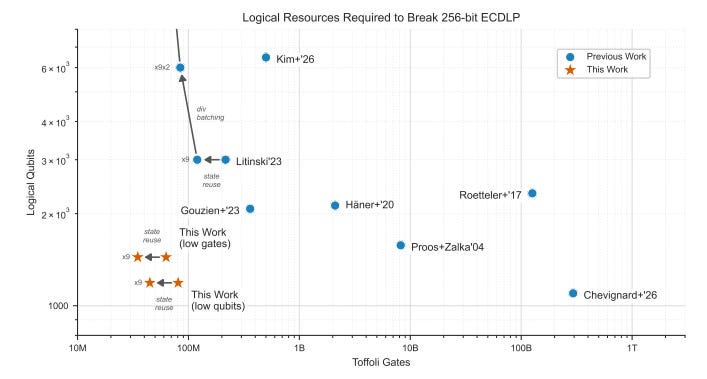
It’s significant because it is now estimated that less time on a less powerful quantum computer will eventually be needed to break ECC, a widely used cryptographic scheme that secures much of the Internet and digital protocols.
It’s also noteworthy that, instead of publicly releasing the quantum circuit, the team used zero-knowledge proofs to verify the circuits without disclosing their contents.
Zero-knowledge proofs (zk proofs) are cryptographic methods by which one party can prove to another that something is true, without revealing any information.
So how do we verify that these quantum circuits exist?
This article explains the circuits and focuses on answering this exact question: how to independently verify these zk proofs and confirm that these “private” quantum circuits exist.
Why use zero-knowledge proofs
Industry leaders highlight the growing use of zk proofs to conceal important quantum circuits, emphasizing the need to understand and verify them.
It suggests an emerging trend that researchers want to commercialize circuits, or keep them away from, or face government pressure to withhold them from bad actors.
The white paper states they are not releasing circuits publicly, unlike previous researchers, as bad actors could use them once practical quantum computers are available:
However, the escalating risk that detailed cryptanalytic blueprints could be weaponized by adversarial actors necessitates a shift in disclosure practices.
Justin Drake, co-author of the white paper and researcher at the Ethereum Foundation, suggested that more valuable, important circuits will remain unpublished:
From now on, assume state-of-the-art algorithms will be censored. There may be self-censorship for moral or commercial reasons, or because of government pressure. A blackout in academic publications would be a tell-tale sign.
Nic Carter, a major Bitcoin investor and co-founder of Castle Island Ventures, compares the use of a zk proof to the classification of nuclear research, as the atomic bomb was developed:
This [use of zero-knowledge proofs to conceal the quantum circuits from Google Quantum AI] recalls what happened in the physics community in the lead up to the development of the atomic bomb. In 1940, the National Academy of Sciences voluntarily adopted a self-censorship regime. Once the Manhattan Project began, all formal publications ceased. In July 1945, the first fission bomb was detonated in the White Sands missile range, New Mexico.
It becomes critical to understand how to verify them, as more researchers adopt zk proofs to hide, yet “prove” specific quantum circuits exist.
What Google’s quantum circuits mean
Google Quantum AI researchers provided the metadata for two quantum circuits capable of breaking ECC.
A circuit is considered capable of breaking ECC if it can solve 9,024 elliptic curve point addition problems with different starting point inputs.
Given two starting points on an elliptic curve, Points P and Q, the circuit can find the third point, Point (-R), where the line passes through P and Q intersects with the curve. Then, it computes Point R by reflecting Point (-R) across the x-axis. R is reflected as the sum, or addition, of P and Q.
In more mathematically direct terms:
correctly computes point addition on the elliptic curve secp256k1 [the type of elliptic curve used in Bitcoin] across all 9,024 pseudo-random inputs deterministically derived from the circuit’s own hash
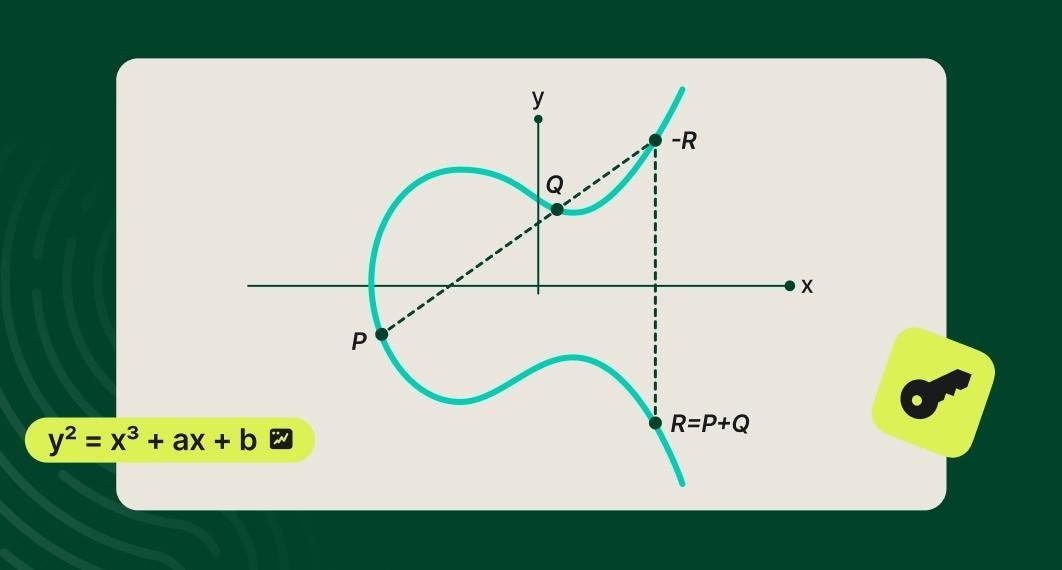
Most elliptic curves are less uniform than this example, and it is not obvious to an everyday, classical computer where the third point lies, which makes ECC traditionally very secure for encrypting digital data, as explained in this video:
Therefore, solving 9,024 of these problems is no easy task. Quantum circuits that can solve 9,024 instances, as the researchers at Google Quantum AI claimed, show it can reliably perform the elliptic curve arithmetic required for a full ECC attack.
Google Quantum AI presented detailed information on two circuits that satisfied this criterion; each circuit was optimized for distinct objectives.
The first approach uses fewer qubits, or quantum computing units, making it more optimized for hardware limitations.
The second uses fewer gates or computing operations, making it more optimized for runtime performance.
Having two circuits optimized for different objectives allows them to be run on various types of quantum computers better suited to specific tasks, such as hardware or performance.
Circuit metadata
Although these quantum circuits require as few as 70–80 percent fewer resources than other circuits capable of breaking ECC, they are still too large to run as programs on a quantum computer. Their performance remains based on theoretical assumptions, although they should not be ignored.
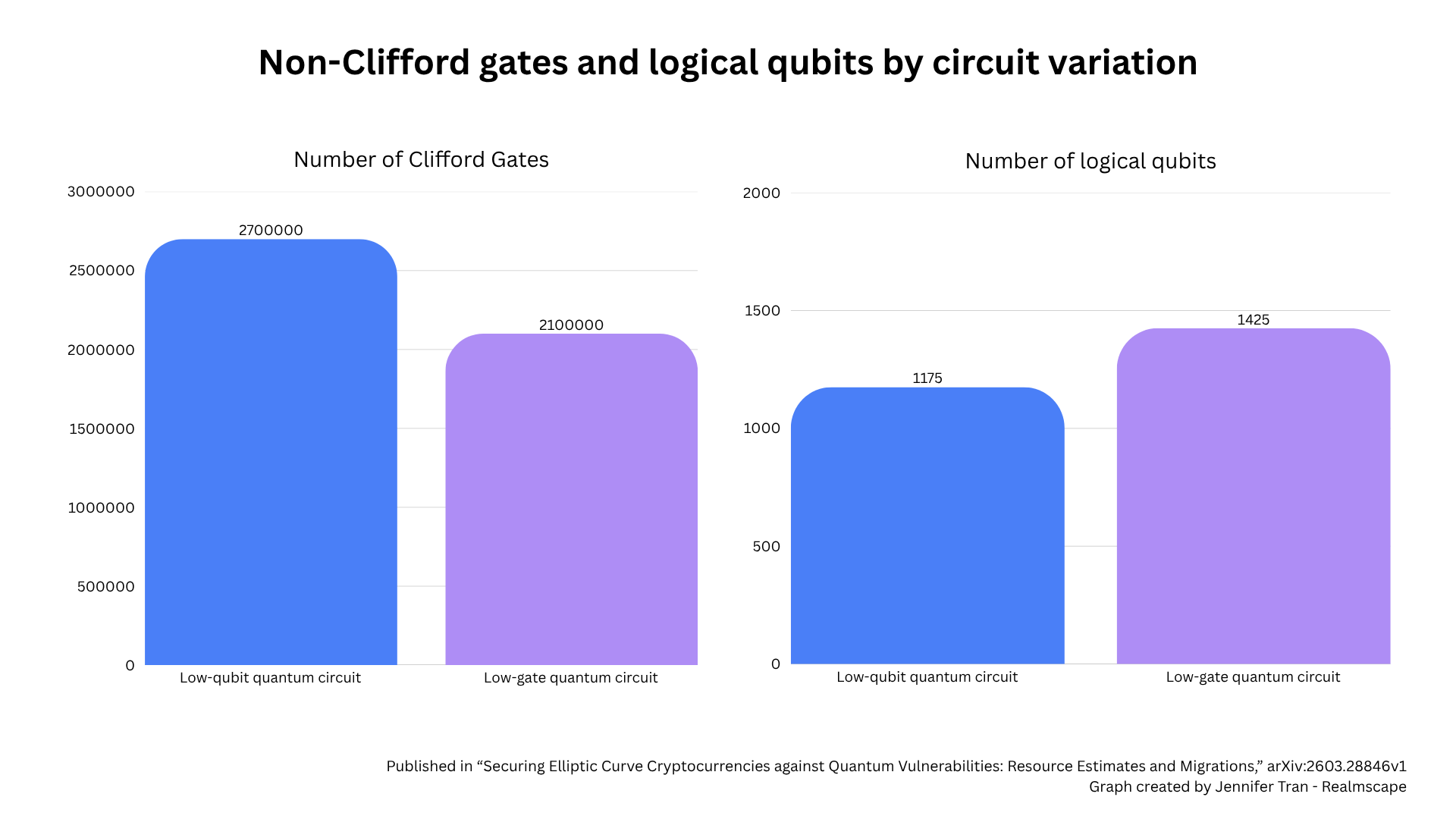
The circuit metadata included the number of non-Clifford gates, which are operations required for universal quantum computation, and the number of logical qubits, which are qubits that carry out computation while being protected from noise and errors by many surrounding physical qubits.
The quantum circuit with fewer qubits, or the “low-qubit quantum circuit,” included:
2,700,000 non-Clifford gates
1,175 logical qubits
The quantum circuit with fewer gates, or the “low-gate quantum circuit,” included:
2,100,000 non-Clifford gates
1,425 logical qubits
Verifying the metadata
How the zero-knowledge proof was created
A zero-knowledge proof was generated for each quantum circuit, yielding three assigned identifiers for verifying its metadata.
Here are identifiers for the low-qubit quantum circuit presented in the white paper:
Circuit SHA-256 Hash:
0xcc8f532ffea1583ceed3c9af75de3263ebaddd5fdf3cddfb3dea848b94d0396a
Verification Key:
0x00ca4af6cb15dbd83ec3eaab3a0664023828d90a98e650d2d340712f5f3eb0d4
Groth16 Proof Bytes:
0x0e78f4db0000000000000000000000000000000000000000000000000000000000000000008cd56e10c2fe24795cff1e1d1f40d3a
324528d315674da45d26afb376e86700000000000000000000000000000000000000000000000000000000000000000215c7fe4fc59
7b861d82370ab556684ae36e98cf073e7f754f2788ad58721dbd012927516f316e7b4f3effb1dbd567732611cb0334f2d75e529c5e3
becd0629c17605c7ff87c6f23324328744454bdec0df425a4a63e3358c10079c85ef757412ae86ae1f85bf47ef6980852d6f65423be
2d90adb5b29896493324128b1cda0a0042f7138c850a1ca441210ba770a2eee39d56f6f90bf68b7a346e1658c6529715334621b6e1a
63b85875b8c8a610e0d885662879755803027dad57d97140afb2498bbb63215b236575f95b0019f2b9713bc810e1e044d47ab360e92
b899c46512fc97460609186bf1fe01c892a8015fb00e7fdea11b08f88c6adb79b1243518And the identifiers for the low-gate quantum circuit:
Circuit SHA-256 Hash:
0x24f5758f2216aa87aa2806af32a0db788767b873cf6869510cca3d893b3f8a69
Groth16 Proof (Hex):
0x0e78f4db0000000000000000000000000000000000000000000000000000000000000000008cd56e10c2fe24795cff1e1d1f40d3a
324528d315674da45d26afb376e867000000000000000000000000000000000000000000000000000000000000000000a11fe07d3af
e9d5e9b5af9fdb37fc38bd529d09b92e08350556a3a38ad03f1b2ed337741ecfeae1a65849d1927cdfc3ea4d211734cd747fc4a5534
449ebfd1e2130fde87661e0e0fba6ec2055c130d875c7fa3358e25e2236e928520eddfa992a9e6510d0635161c62e0e29f4c28921f5
6126a908b286c4d910089780441a5811799d5c7dbf293ac3e6d5f51267efbf95cf8643cb28c5f7c2bac8ee9d4b55c830475b328ff9f
9b257f2383e7934aaab12616e04645bf6a2b9820cafba4fd3830655d676b7ff376817bbd18a178cf091ad4f4e53b2e322a1d75b3e14
00d9b66e1feb401eae0df274d7a774f0bd2fc471ce574348daeaac3ee288dcd282456a33
Verification Key:
0x00ca4af6cb15dbd83ec3eaab3a0664023828d90a98e650d2d340712f5f3eb0d4Circuit SHA-256 Hash
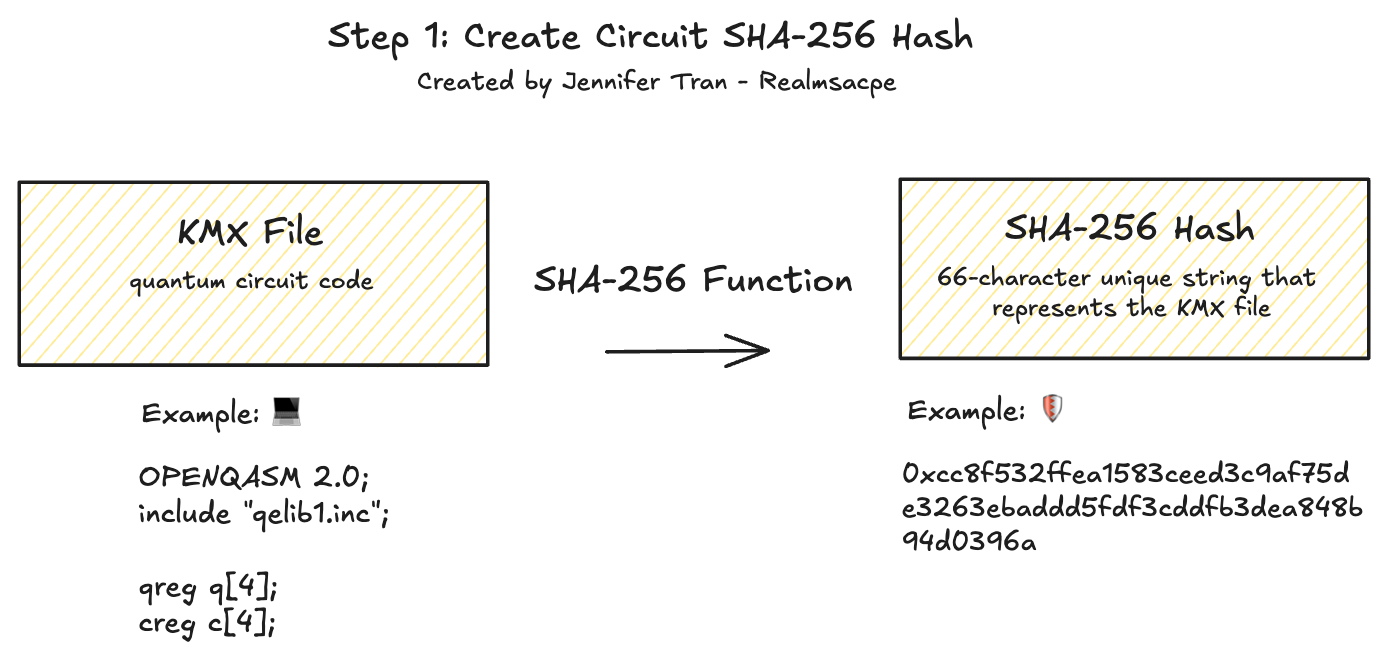
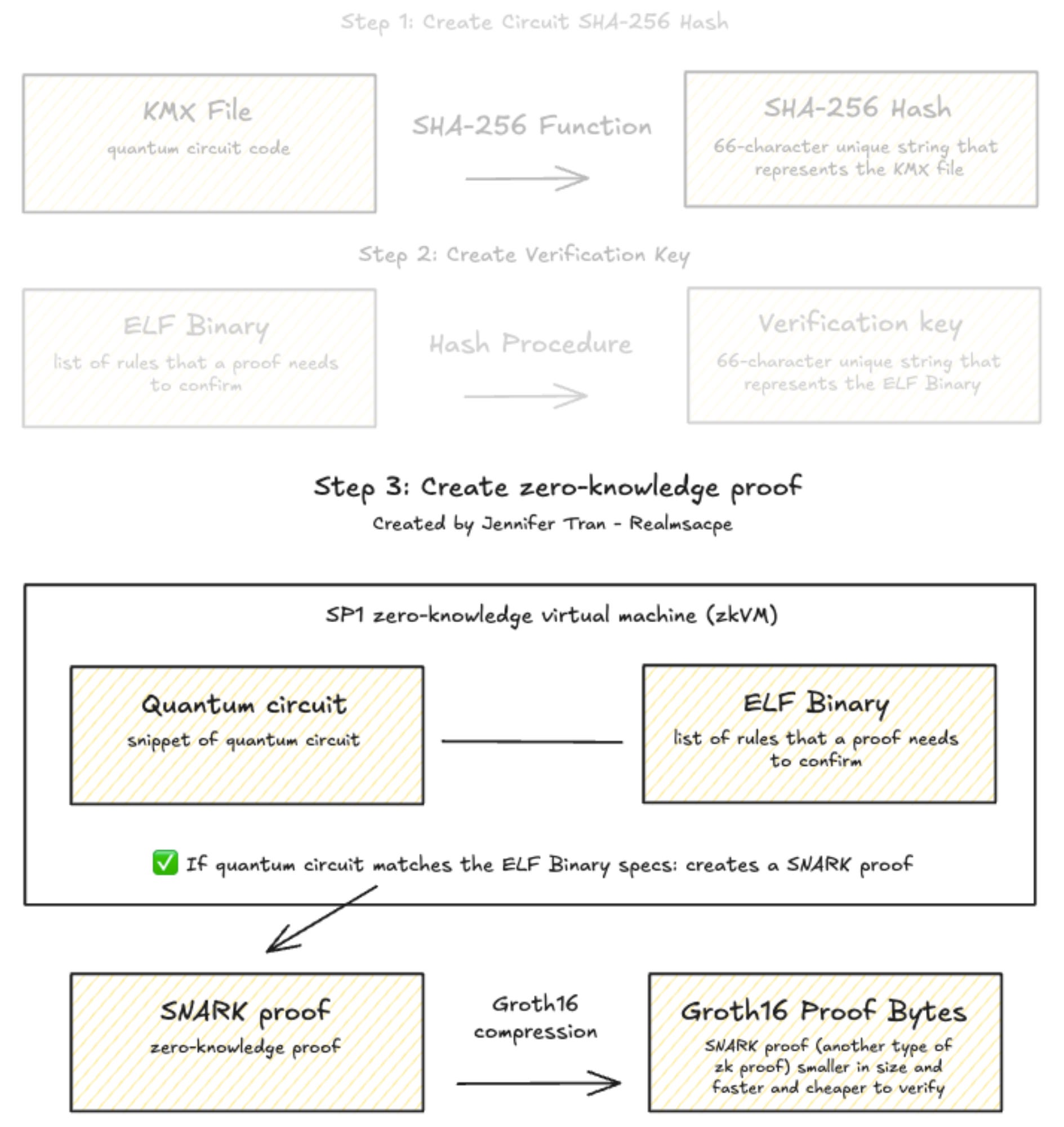
First, researchers created a Circuit SHA-256 Hash for each circuit.
The KMX file containing the quantum circuit code was converted to a “hash,” or unique 66-character string, using the SHA-256 function. SHA-256 hashes cannot be easily reversed to reveal the original text.
Groth16 Proof Bytes and Verification Key
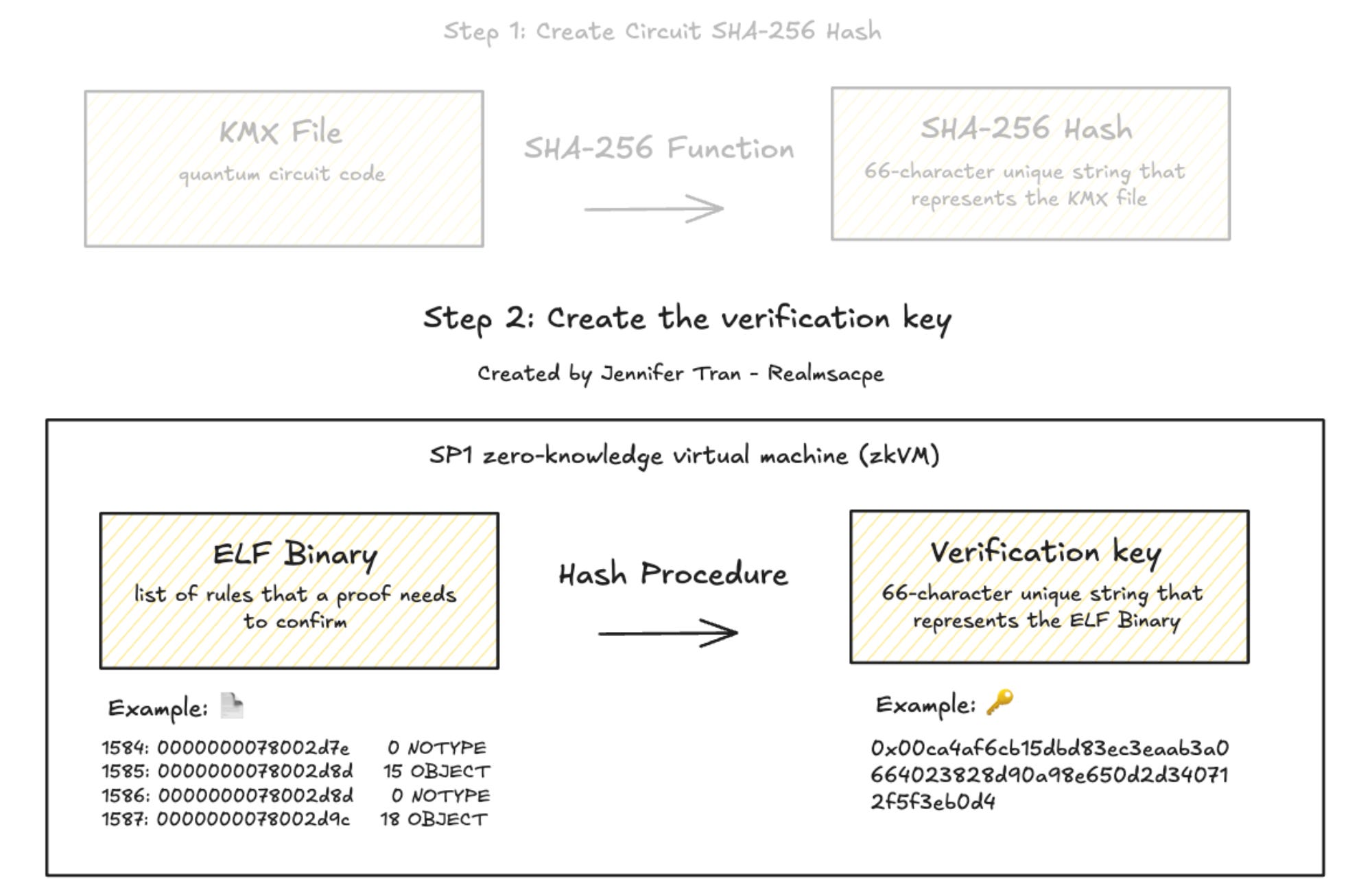
Then, researchers created an ELF binary, a list of rules that a zero-knowledge proof needed to “prove” or validate.
The ELF binary is a RISC-V program written in assembly language or C/C++, and the code must reflect an example statement such as this that proves the quantum circuit exists:
Zero Knowledge Proof Statement 1 (Low-Qubit Variant)
We possess a quantum kickmix circuit C low-qubit (uniquely committed to via its cryptographic hash) with resource counts of at most:
2,700,000 non-Clifford gates (CCX + CCZ)
1,175 logical qubits
17,000,000 total operations
that correctly computes point addition on the elliptic curve secp256k1 across all 9,024 pseudo-random inputs deterministically derived from the circuit’s own hash.
This introduces a significant trust assumption. Readers must trust that researchers created an honest and accurate ELF binary, since the circuits are hidden. Independent audits of ELF binaries are critical, but none have been conducted yet (though I’ve considered doing one myself; tools such as Ghidra can be used to evaluate ELF binaries).
Then, researchers used the ELF binary and the circuit to verify that the circuit met all the rules specified in the ELF binary.
Researchers would run the ELF binary with the circuit as its input inside a SP1 zero-knowledge virtual machine (zkVM), a sandboxed computing environment developed by Succinct Labs that executes instructions (such as those in an ELF binary), verifies computations, and produces zero-knowledge cryptographic proofs upon verification.
In this case, first, the zkEVM processed the ELF binary and hashed it to create a verification key.
Then, the zkVM followed the ELF binary instructions to check that the circuit correctly computed elliptic curve point addition across all 9,024 test inputs.
Upon verification, the zkEVM generated a STARK proof, a (yes, post-quantum secure) cryptographic string confirming verification and cross-checkable with the verification key and ELF binary.
An original STARK proof is relatively large and slower to verify, so it was compressed into Groth16 Proof Bytes, a version of a SNARK (another class of zero-knowledge proofs) that is smaller and cheaper to verify.
Anyone can use the Groth16 Proof Bytes together with the verification key in Step 2 to verify the result in milliseconds without the original circuit, re-computation, or trusting researchers.
How to independently verify the proof
The easiest way to verify the proof is to use the provided identifiers and the verification program in the public Zenodo archive, a general-purpose open repository for research and data that is usable on any typical computer. I ran the upcoming terminal commands on my Mac laptop.
Verifying the proof confirms that quantum circuits exist that satisfy the requirements defined in the ELF binary. These requirements were to solve 9,024 elliptic curve addition problems within the resource limits specified for the low-qubit and low-gate quantum circuits described in the Google Quantum AI white paper.
It does not confirm that the quantum circuits were successfully executed on a quantum computer (which they were not) or that the ELF binary had the correct verification logic and properly checked the quantum circuits.
Step 1: Download zkp_ecc_zenodo.zip from the provided Zenodo archive and extract it.
The directory structure should contain:
zkp_ecc_zenodo/
├── verifier/
│ ├── verifier.rs ← the verification program
│ └── Cargo.toml ← its dependencies
├── proofs/
│ ├── zkp_ecc-program ← the ELF binary
│ ├── vkey.bin ← the verification key
│ ├── low_qubits/
│ │ └── proof_9024.bin ← proof for the low-qubit circuit
│ └── low_toffoli/
│ └── proof_9024.bin ← proof for the low-gate circuit
└── run_proofs.sh ← script for regenerating proofs (requires GPUs)The five most important files are:
proofs/zkp_ecc-program: the ELF binary
proofs/vkey.bin: the verification key
proofs/low_qubits/proof_9024.bin: Groth16 Proof Bytes for the low-qubit circuit
proofs/low_toffoli/proof_9024.bin: Groth16 Proof Bytes for the low-gate circuit
verifier.rs: the verification program, which will be explained further in the following sections
Step 2: Install the dependencies
The verifier is written in Rust and depends on the SP1 SDK, which depends on protobus for its data serialization format.
brew install protobufStep 3: Review the verifier.rs, the verification program
The verification program, found at verifier/verifier.rs, confirms that the zk proof corresponds to a valid execution of the verification logic.
In other words, it verifies that the circuit was evaluated according to the ELF binary and satisfied the claimed specifications of the quantum circuits, as explained in the “How the zero-knowledge proof was created” section.
It does this by checking the Groth16 Proof Bytes against the verification key, which is the compressed representation of the ELF binary constraints.
First, it reads the verification key:
let vk_bytes = std::fs::read(&vkey_path).expect("failed to read vkey file");Then, it loads the Groth16 Proof Bytes:
let mut proof = SP1ProofWithPublicValues::load(&args.proof).expect("failed to load proof");It uses the SP1 SDK to verify the proof against the verification key.
client.verify(&proof, &vk, None).expect("failed to verify proof");If the verification succeeds, it returns an output as shown in Step 5.
Step 4: Run the verifier
Once the verification logic is understood, the program can be executed to check the proof.
The verification program requires two inputs: Groth16 Proof Bytes and the verification key of a specific circuit.
Low-qubit circuit
In the case of the low-qubit circuit, the Groth16 Proof Bytes are stored in proofs/low_qubits/proof_9024.bin. Run the verifier within the zkp_ecc_zenodo folder for the low-qubit circuit with this command:
RUST_LOG=info cargo run --release -p verifier -- \
--proof proofs/low_qubits/proof_9024.bin \
--vkey proofs/vkey.binLow-gate circuit
In the case of the low-qubit circuit, the Groth16 Proof Bytes are stored in proofs/low_toffoli/proof_9024.bin. Run the verifier within the zkp_ecc_zenodo folder for the low-qubit circuit with this command:
RUST_LOG=info cargo run --release -p verifier -- \
--proof proofs/low_toffoli/proof_9024.bin \
--vkey proofs/vkey.binStep 5: Review the output
If the verification succeeds, the verification program confirms that the zk proof corresponds to the valid execution of the verification logic and returns an output.
The output should match the provided metadata for each circuit.
✅ Low-qubit circuit:
Circuit SHA-256 Hash / Circuit hash commitment:
0xcc8f532ffea1583ceed3c9af75de3263ebaddd5fdf3cddfb3dea848b94d0396aVerification Key / Verifying Key (Hex)):
0x00ca4af6cb15dbd83ec3eaab3a0664023828d90a98e650d2d340712f5f3eb0d4Non-Clifford gates / Demanded Average non-Clifford count: 2,700,000
Logical qubit count / Demanded Qubit count: 1,175 logical qubits
Output:
Verifying Key (Hex): 0x00ca4af6cb15dbd83ec3eaab3a0664023828d90a98e650d2d340712f5f3eb0d4
Proof (Hex): 0x0e78f4db0000000000000000000000000000000000000000000000000000000000000000008cd56e10c2fe24795cff1e1d1f40d3a324528d315674da45d26afb376e86700000000000000000000000000000000000000000000000000000000000000000215c7fe4fc597b861d82370ab556684ae36e98cf073e7f754f2788ad58721dbd012927516f316e7b4f3effb1dbd567732611cb0334f2d75e529c5e3becd0629c17605c7ff87c6f23324328744454bdec0df425a4a63e3358c10079c85ef757412ae86ae1f85bf47ef6980852d6f65423be2d90adb5b29896493324128b1cda0a0042f7138c850a1ca441210ba770a2eee39d56f6f90bf68b7a346e1658c6529715334621b6e1a63b85875b8c8a610e0d885662879755803027dad57d97140afb2498bbb63215b236575f95b0019f2b9713bc810e1e044d47ab360e92b899c46512fc97460609186bf1fe01c892a8015fb00e7fdea11b08f88c6adb79b1243518
Successfully verified Groth16 SNARK proof.
Circuit hash commitment: 0xcc8f532ffea1583ceed3c9af75de3263ebaddd5fdf3cddfb3dea848b94d0396a
Demanded Number of tests: 9024
Demanded Qubit count: 1175
Demanded Average non-Clifford count: 2700000
Demanded Total ops: 17000000✅ Low-gate circuit:
Circuit SHA-256 Hash / Circuit hash commitment:
0x24f5758f2216aa87aa2806af32a0db788767b873cf6869510cca3d893b3f8a69Verification Key / Verifying Key (Hex):
0x00ca4af6cb15dbd83ec3eaab3a0664023828d90a98e650d2d340712f5f3eb0d4Non-Clifford gates / Demanded Average non-Clifford count: 2,100,000
Logical qubit count / Demanded Qubit count: 1,425 logical qubits
Output:
Verifying Key (Hex): 0x00ca4af6cb15dbd83ec3eaab3a0664023828d90a98e650d2d340712f5f3eb0d4
Proof (Hex): 0x0e78f4db0000000000000000000000000000000000000000000000000000000000000000008cd56e10c2fe24795cff1e1d1f40d3a324528d315674da45d26afb376e867000000000000000000000000000000000000000000000000000000000000000000a11fe07d3afe9d5e9b5af9fdb37fc38bd529d09b92e08350556a3a38ad03f1b2ed337741ecfeae1a65849d1927cdfc3ea4d211734cd747fc4a5534449ebfd1e2130fde87661e0e0fba6ec2055c130d875c7fa3358e25e2236e928520eddfa992a9e6510d0635161c62e0e29f4c28921f56126a908b286c4d910089780441a5811799d5c7dbf293ac3e6d5f51267efbf95cf8643cb28c5f7c2bac8ee9d4b55c830475b328ff9f9b257f2383e7934aaab12616e04645bf6a2b9820cafba4fd3830655d676b7ff376817bbd18a178cf091ad4f4e53b2e322a1d75b3e1400d9b66e1feb401eae0df274d7a774f0bd2fc471ce574348daeaac3ee288dcd282456a33
Successfully verified Groth16 SNARK proof.
Circuit hash commitment: 0x24f5758f2216aa87aa2806af32a0db788767b873cf6869510cca3d893b3f8a69
Demanded Number of tests: 9024
Demanded Qubit count: 1425
Demanded Average non-Clifford count: 2100000
Demanded Total ops: 17000000Conclusion
Google Quantum AI researchers developed quantum circuits capable of breaking ECC that are not publicly released, but are verifiable using zero-knowledge proofs.
Researchers may increasingly rely on zk proofs to commercialize circuits, prevent misuse, or respond to government pressure while still publicly demonstrating that they have made a breakthrough.
Running the verifier confirms that quantum circuits exist that satisfy the statements committed to in the proof. However, it does not confirm that the quantum circuits were ever successfully run on a quantum computer or that the ELF binary itself contains the correct verification logic.
As more researchers use zero-knowledge proofs to support claims about undisclosed quantum circuits, independent verification and audits of proofs will become increasingly important.